
I have recently been working with a customer to upgrade to Exchange Server 2016, one of the requirements is to enable TLS 1.2. The following will guide you through the preparation, implementation and then testing.
For the testing I have used ZenMap/NMAP: – https://nmap.org/download.html
Preparation
Exchange Server 2016
- Install Cumulative Update (CU) 8 in production for TLS 1.2 support and be ready to upgrade to CU9 after its release if you need to disable TLS 1.0 and TLS 1.1. –CU 10 is now available.
- Install the newest version of .NET and associated patches supported by your CU (currently 4.7.2).
Exchange Server 2013
- Install CU19 in production for TLS 1.2 support and be ready to upgrade to CU20 after its release if you need to disable TLS 1.0 and TLS 1.1.
- Install the newest version of .NET and associated patches supported by your CU (currently 4.7.2).
Windows Server 2016
- TLS 1.2 is the default security protocol for Schannel and consumable by WinHTTP.
- Ensure you have installed the most recent Monthly Quality Update along with any other offered Windows updates.
Windows Server 2012 R2
- TLS 1.2 is the default security protocol for Schannel and consumable by WinHTTP
- Ensure your server is current on Windows Updates.
- This should include security update KB3161949 for the current version of WinHTTP.
- If you rely on SHA512 certificates; please see KB2973337.
Windows Server 2012
- TLS 1.2 is the default security protocol for Schannel.
- Ensure your server is current on Windows Updates.
- This should include security update KB3161949 for the current version of WinHTTP.
- If you rely on SHA512 certificates; please see KB2973337.
Implementation
Enable TLS 1.2 for Schannel
To enable TLS 1.2 for both server (inbound) and client (outbound) connections on an Exchange Server please perform the following.
- From Notepad.exe, create a text file named TLS12-Enable.reg.
- Copy and paste the following text into the file.
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\ Protocols\TLS 1.2] [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\ Protocols\TLS 1.2\Client] "DisabledByDefault"=dword:00000000 "Enabled"=dword:00000001 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\ Protocols\TLS 1.2\Server] "DisabledByDefault"=dword:00000000 "Enabled"=dword:00000001
- Save TLS12-Enable.reg.
- Double-click the TLS12-Enable.reg file.
- Click Yes to update your Windows Registry with these changes.
- Restart the machine for the changes to take effect.
Enable TLS 1.2 for .NET 4.x
This step is only required for Exchange Server 2013 or later installations where .NET 4.x is relied upon.
The SystemDefaultTlsVersions registry value defines which security protocol version defaults will be used by .NET Framework 4.x. If the value is set to 1, then .NET Framework 4.x will inherit its defaults from the Windows Schannel DisabledByDefault registry values. If the value is undefined, it will behave as if the value is set to 0. By configuring .NET Framework 4.x to inherit its values from Schannel we gain the ability to use the latest versions of TLS supported by the OS, including TLS 1.2.
- From Notepad.exe, create a text file named NET4X-UseSchannelDefaults.reg.
- Copy, and then paste the following text.
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\.NETFramework\v4.0.30319] "SystemDefaultTlsVersions"=dword:00000001 [HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\.NETFramework\v4.0.30319] "SystemDefaultTlsVersions"=dword:00000001
- Save the NET4X-UseSchannelDefaults.reg file.
- Double-click the NET4X-UseSchannelDefaults.reg file.
- Click Yes to update your Windows Registry with these changes.
- Restart your computer for the change to take effect.
Note: When configuring a system for TLS 1.2, you can make the Schannel and .NET registry keys at the same time and reboot the server once.
Testing
Testing before TLS has been enabled (the default state of an Exchange 2016 Deployment) using ZenMap
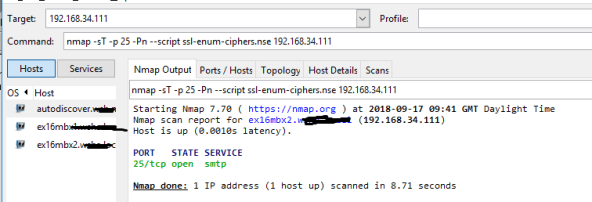
Testing after TLS has been enabled (after following the above procedures) using ZenMap

Message Headers (Exchange Server 2016 Only)
Message header data in Exchange Server 2016 provides the protocol negotiated and used when the sending and receiving host exchanged a piece of mail. While this is a more manual method of checking how mail arrived it can be used for testing between specific systems in a pinch.
Example when viewing message header data via Message Header Analyzer at https://testconnectivity.microsoft.com
Mail Flow via SMTP Logging
SMTP Logs in Exchange 2016 will contain the encryption protocol and other encryption related information used during the exchange of email between two systems.
When the server is the SMTP receiving system, the following strings exist in the log depending on the version of TLS used.
-
TLS protocol SP_PROT_TLS1_0_SERVER
-
TLS protocol SP_PROT_TLS1_1_SERVER
-
TLS protocol SP_PROT_TLS1_2_SERVER
When the server is the SMTP sending system, the following strings exist in the log depending on the version of TLS used.
-
TLS protocol SP_PROT-TLS1_0_CLIENT
-
TLS protocol SP_PROT-TLS1_1_CLIENT
-
TLS protocol SP_PROT-TLS1_2_CLIENT
