
I have recently been working on a project to move nearly 2000 users from one Office 365 tenant to another. You may say simple, there are plenty of third party tools out there that will do that for you, but what about if the customer has not budgeted for the extra cost for these tools…. What do you do?
Now in this solution we had to purchase a very cost effective tool and a SSL certificate for the Exchange Server. The costs for these were no where near the costs of all of the well known tools from BitTitan and Cloud Migrator. we were quoted $6 per user by BitTitan as it was education or for normal businesses we were quote $14 per user. So as you would expect approx 2000 licenses at $6 each works out very expensive for an unexpected cost.
The tool we used was called Systools OneDrive Migrator and as you can see the tool cost starts from $99. We ended up paying $1 per user for this product. So a massive saving on the total cost of the tool from other competitors.
Stage 1 – Build a On Premise Hybrid Server
Download the latest Exchange 2016 ISO from here: Exchange Download
Before you deploy the On Premise Exchange Server you need to make sure your AD infrastructure is in good shape and able to support the deployment of Exchange 2016, so you need to ensure that the Forest and Domain Functional Levels are at least Windows Server 2008 R2
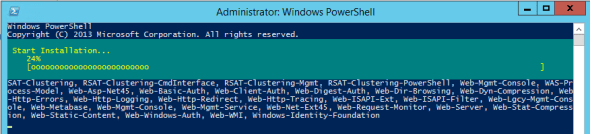
Before you begin to install Exchange Server 2016 you will need to install the Windows Server Roles and Features… Below is the PowerShell to ensure that all Windows Features are deployed:
Windows Server 2012 and 2012 R2
Install-WindowsFeature AS-HTTP-Activation, Desktop-Experience, NET-Framework-45-Features, RPC-over-HTTP-proxy, RSAT-Clustering, RSAT-Clustering-CmdInterface, RSAT-Clustering-Mgmt, RSAT-Clustering-PowerShell, Web-Mgmt-Console, WAS-Process-Model, Web-Asp-Net45, Web-Basic-Auth, Web-Client-Auth, Web-Digest-Auth, Web-Dir-Browsing, Web-Dyn-Compression, Web-Http-Errors, Web-Http-Logging, Web-Http-Redirect, Web-Http-Tracing, Web-ISAPI-Ext, Web-ISAPI-Filter, Web-Lgcy-Mgmt-Console, Web-Metabase, Web-Mgmt-Console, Web-Mgmt-Service, Web-Net-Ext45, Web-Request-Monitor, Web-Server, Web-Stat-Compression, Web-Static-Content, Web-Windows-Auth, Web-WMI, Windows-Identity-Foundation, RSAT-ADDS
Windows Server 2016
Install-WindowsFeature NET-Framework-45-Features, RPC-over-HTTP-proxy, RSAT-Clustering, RSAT-Clustering-CmdInterface, RSAT-Clustering-Mgmt, RSAT-Clustering-PowerShell, Web-Mgmt-Console, WAS-Process-Model, Web-Asp-Net45, Web-Basic-Auth, Web-Client-Auth, Web-Digest-Auth, Web-Dir-Browsing, Web-Dyn-Compression, Web-Http-Errors, Web-Http-Logging, Web-Http-Redirect, Web-Http-Tracing, Web-ISAPI-Ext, Web-ISAPI-Filter, Web-Lgcy-Mgmt-Console, Web-Metabase, Web-Mgmt-Console, Web-Mgmt-Service, Web-Net-Ext45, Web-Request-Monitor, Web-Server, Web-Stat-Compression, Web-Static-Content, Web-Windows-Auth, Web-WMI, Windows-Identity-Foundation, RSAT-ADDS
When the pre reqs are installing it will look something like this:
You then need to prepare the your AD Environment by running the following commands:
setup o /prepareschema
o /prepareAD
o /preparealldomains
/iacceptexchangeserverlicenseterms
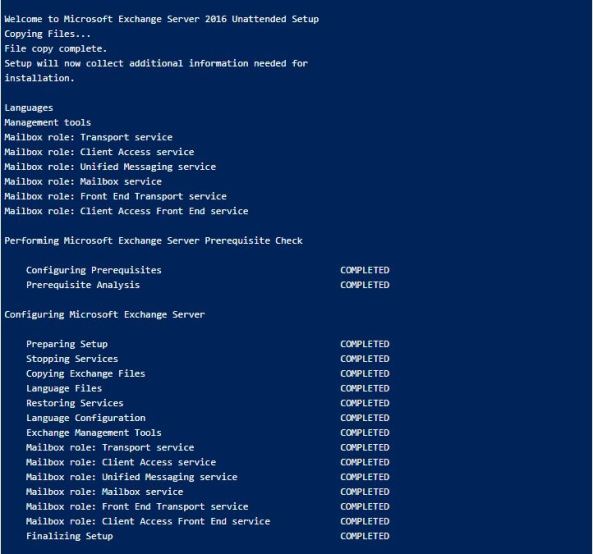
and then to begin the installation of Exchange 2016 you need to run the following:
setup /m:install /r:mailbox /iacceptexchangeserverlicenseterms
A successful Exchange Installation will look like this:
Stage 2 – AAD Connect
A Guide for deploying AAD Connect can be found here
Key things to take into consideration are to ensure the following:
1, The AD Account UPNs match that of the email address of the user
2, When you deploy AAD Connect the following options must be chosen in order for the Exchange Hybrid to work correctly:

Stage 3 – Update all the users in Active Directory to have some Exchange attributes
The first thing you need to do is collect information about the online mailbox that you are looking to move. The information you need is the Mailbox Alias The User Principal Name and the Mailbox Guid. To get this information and output it to a CSV file run the following script in your Exchange Online Shell.
Get-Mailbox -ResultSize Unlimited | Select-Object Alias,UserPrincipalName,ExchangeGUID | Export-Csv -Path c:\temp\userExport.csv -NoTypeInformation
Once you have exported the above information you will need to move over to you On Premise Exchange Server and the Exchange Management Shell and run the following command that update all of the Active Directory objects with the required Exchange Attributes:
$allUsers = Import-Csv C:\temp\userExport.csv
foreach ($user in $allUsers) { Enable-RemoteMailbox $user.alias
-RemoteRoutingAddress "$($user.alias)@tenant.mail.onmicrosoft.com";
Set-RemoteMailbox $user.alias -ExchangeGuid $user.ExchangeGuid
-EmailAddressPolicyEnabled $false -PrimarySmtpAddress
"$($user.alias)@bscmail.org" }
When you go into the Exchange Management Centre and look at the mailboxes you will be able to see all of your Exchange Online Mailboxes listed in your On Prem Exchange Server.
Stage 4 – Migrate mailboxes to Exchange 2016
Prepare the Hybrid Configuration
Details for configuring and Exchange Hybrid based on your on prem Exchange Server can be found here:
Migrate Mailboxes to the Hybrid Server
Steps to migrate mailboxes from Exchange Online can be found here:
Stage 5 – Migrate mailboxes to the other Office 365 Tenant
Re point the Hybrid connection to the new Office 365 Tenant
All the hard work would have been done in the previous section about creating the hybrid. – all you need to do here is re run the hybrid configuration wizard and point it at the new Office 365 tenant.
Migrate mailboxes to Office 365
Steps to move mailboxes back to Office 365 can be found here
https://docs.microsoft.com/en-us/exchange/hybrid-deployment/move-mailboxes
Stage 6 – Preparing OneDrive For Business for Migration
In order for us to be able to migrate data from OneDrive for business we will need to configure user interpretation on all of the users OneDrive sites. To do this the following steps need to be followed:
Assign eDiscovery permissions to OneDrive for Business Sites – Follow this guide from Microsoft:
Once this has been done, the user that will be used to the data migration will have sufficient access to the users OneDrive for Business sites.
Stage 7 Migrating OneDrive For Business to the new Tenant
This stage is rather like the previous one. However you will need to ensure that all the users OneDrive sites have been provisioned, unfortunately just by allocating a license to the user does not automatically provision, so there is a script that needs to be run in order to force the provisioning to take place. This also takes some time to do depending on how many users there are.
1, Provision OneDrive For Business Sites in new Tenant
https://docs.microsoft.com/en-us/onedrive/pre-provision-accounts
2, Assign eDiscovery permissions to OneDrive for Business – New Tenant (destination)
3, Run the Systools Migration Tool to move the data between the tenants. – Make sure your CSV files that are created with this tool match the users up correctly, as it will be very easy to mix up the user source and destination. – we don’t want users to get the wrong data in their OneDrive sites.
Download & Install SysTools OneDrive Migrator Tool.
 Now provide the ID for the first Onedrive account. CLick on the “Login” button:
Now provide the ID for the first Onedrive account. CLick on the “Login” button:
 Now, The tool will redirect to a browser window where you have to provide the password for the same.
Now, The tool will redirect to a browser window where you have to provide the password for the same.

Now, Provide the credentials for the second account as follows:

Click on the “Import CSV” button in order to add a csv file containing all the id that are to be added to the CSV file.
 Navigate and select the location for the CSV file as follows:
Navigate and select the location for the CSV file as follows:

The Ids will be displayed as follows in the following section:
 Click on the “Next” button.
Click on the “Next” button.

Now, Provide the filters in the following section as follows:
Provide the permissions for which the files are to be transferred on the respective ids:
 Click on the “Import CSV” button.
Click on the “Import CSV” button.
Go to the Date filterto provide the calendar interval according to which the data should be transferred.

Click on “Advanced Settings” and check mark the check box correspoding to the text include file type as follows:
 Click on the “Export” button.
Click on the “Export” button.
The export process will start as follows:
 The conversion will be completed as follows:
The conversion will be completed as follows:

Click on the “Save Report” to save the export report for the process:
 Navigate the location for the final export report file:
Navigate the location for the final export report file:
 The export report will be saved successfully.
The export report will be saved successfully.

The export report can be viewed as follows:
 The final migrated can also be viewed as:
The final migrated can also be viewed as:



