Wow, time flies when you are having fun….I can’t believe it has been 7 months since my last post.
So since January I have been really busy with numerous projects revolving largely around Office 365 and Exchange. I have picked up some useful knowledge which I will write about here in the coming weeks.
This post is dedicated to something new to me – G-Suite to Office 365 – What a ride this has been! Let me explain how I managed to get it all to hang together and get the two services to exist together during the migration and testing phases.
EMAIL Co Existence / Routing between O365 and G-Suite
This was the tricky bit, how could we get users to co-exist in different services whilst we undertake testing and migrations? There is no connector or hybrid solution like there is with Exchange. We did not want to cut over all the users at the same time – this had to be a phased migration over to Office 365. We are also using MimeCast for SPAM and Relay protection so we need Google & Office 365 to send outbound via Mimecast without any mails getting blocked. Here is how we did it:
Office 365
Office 365 needs to be forwarding mail onto a domain that G-Suite knows about and the users mailboxes need to have an alias address for office 365 to forward onto.
The steps are as follows:
- Add Domain Domain A with MX Record
- Add secondary email address for each user. This needs to be set to: user@domainA.com
For users that are not yet in Office 365 we need to configure the Accepted Domain as an Internal Relay in Mail Flow in Exchange Online Admin Centre

Then we create a connector back to G-Suite for any address that does not live in O365 yet. Doing this tells Exchange Online to send the email to the recipient over in G-Suite.
We then stumbled across another minor problem. In order for the Email Data to be migrated into the new Office 365 users mailbox, we need to activate the license. In doing this creates a Office 365 mailbox so then Office 365 thinks the user is now happily working from Office 365. “WRONG”!!! The user still lives in G-Suite until the migration is completed. So in order for the users in Office 365 to send to a user in G-Suite who’s mailbox is provisioned in O365 we have need to create another forwarder back to G-Suite until the migration is completed. How to do this in bulk is in a following section in the blog post. – Adding Contacts to Office 365.
G-Suite
G-Suite needs to have a forwarder configured that the Tenant does not have the domain registered to. If you register a domain with Google it treats all SUB domains as internal as well, so a completely new unregistered domain is required to forward any Office 365 bound mail to.
In order for Gmail to send a message to a forwarding address, the address needs to be verified. So here is a way to forward to an address that is not verified (added to the G-Suite Tenant):
You will need to apply mappings (aliases) to recipient addresses on messages received by your domain. You can map multiple individual recipient addresses (a maximum of 2,000 entries) to other addresses. An individual address can map to a maximum of twelve addresses.
This is a basic routing concept, sometimes called a virtual user table, that’s frequently used in mail routing situations to redirect mail from one address to another. By using this setting you don’t need to create individual routing settings for each address mapping.
Configure the Recipient address map setting for your domain:
-
-
From the Admin console Home page, go to
Apps G Suite
G Suite Gmail
Gmail Advanced settings
Advanced settings.
Tip: To see Advanced settings, scroll to the bottom of the Gmail page.
- At the top of the page, ensure that the top-level org is highlighted.
- Scroll down to the Recipient address map section, or type Recipient address map in the search box:
If the setting’s status is Not configured yet, click Configure (the “Add setting” dialog box displays).
If the setting’s status is Locally applied or Inherited, click Edit to edit an existing setting (the “Edit setting” dialog box displays).
- Enter a short description that will appear within the setting’s summary.
- Under Messages to affect, select All incoming messages or Only external incoming messages.
- Scroll down to Routing options, and select Also route to original destination to send a copy of the message to the new address and also deliver it to the original recipient.
Note: If you don’t select this option, the message is only sent to the new address.
For example, jensmith@solarmora.com is in the address map and the new address is jensmith@gmail.com. If the checkbox is checked, both jensmith@solarmora.com and jensmith@gmail.com will receive a copy of the message. If the checkbox is unchecked, then only jensmith@gmail.com will receive the message.
- Enter address mappings in the box.
Each mapping must include two addresses on a single line, separated by a comma. Place the map-to address after the comma. In the following example, davidb@solarmora.com is the map-to address:
jensmith@solarmora.com, davidb@solarmora.com
Each address must be a complete, specific address, and is case-insensitive. An address can be mapped to multiple map-to addresses. In the following example, jensmith@solarmora.com is mapped to both michellec@solarmora.com and johnd@solarmora.com:
jensmith@solarmora.com, michellec@solarmora.com
jensmith@solarmora.com, johnd@solarmora.com
- Click Add to add the mappings.
- When you’re finished making changes, click Add setting or Save to close the dialog box.
Note: Any settings you add are highlighted on the “Email settings” page.
- Click Save changes at the bottom of the “Email settings” page.
- When you’re finished, click Add Setting (at the bottom of the dialog box).
- Click Save changes (at the bottom of the “Email settings” page) to confirm your changes.
It can take up to an hour for changes to propagate to user accounts. You can track changes in the Admin audit log.
Adding Contacts to Office 365
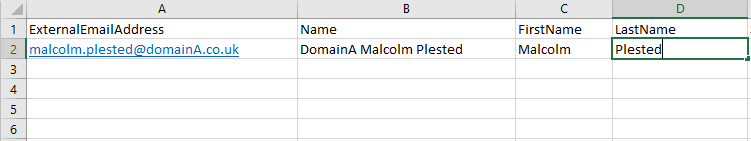
First of all you will need a CSV file like the one in the image below ensuring the column headers match:
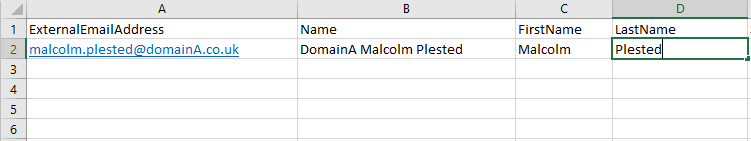
When you have created your list of new Contacts that you need to create you can then import these into Office 365 using the following Powershell Commands:
To Connect to Office 365 Powershell:
Import-Module MSOnline
$O365Cred = Get-Credential
$O365Session = New-PSSession –ConfigurationName Microsoft.Exchange -ConnectionUri
https://ps.outlook.com/powershell -Credential $O365Cred -Authentication Basic
-AllowRedirection
Import-PSSession $O365Session
To import the contacts in your CSV file:
Import-Csv c:\externalcontacts.csv|%
{New-MailContact -Name $_.Name -DisplayName $_.Name -ExternalEmailAddress
$_.ExternalEmailAddress -FirstName $_.FirstName -LastName $_.LastName}
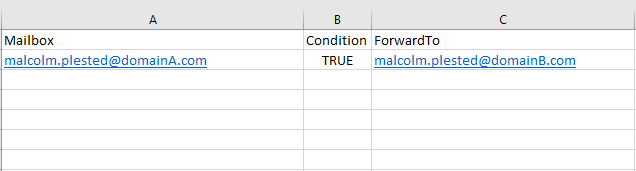
We then had to update all the Office 365 mailboxes to use the forwarding address to send mail back to G-Suite using the following PowerShell and CSV file:
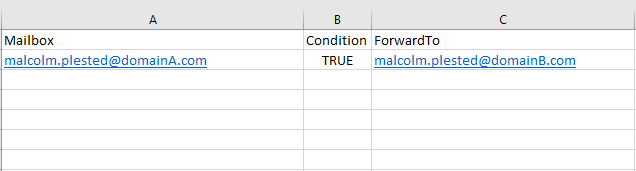
Import-CSV "C:\Temp\Users.csv" | %
{ $_.Condition = [bool]($_.Condition -as [int]); $_ } |
ForEach {Set-Mailbox -Identity $_.mailbox
-ForwardingAddress $_.forwardto -Delivertomailboxandforward
$_.Condition}
On Prem AD with NO Exchange Attributes
So when adding the mailboxes in Office 365 be default the users email addresses were the onmicrosoft.com domain. This was happening because there were no On Premise Exchange Server therefore no Proxy addresses recorded in Active Directory. We then had to add all of the email address alias’s to the proxy addresses using PowerShell. The next few commands are how we did this.
Export the SamAccount and Existing Email details
Import-Module ActiveDirectory
# Delete file if it exists
$FileName = "C:\temp\user.csv"
if (Test-Path $FileName)
{
Remove-Item $FileName
}
Get-Aduser -filter * -Properties * |
Select SamAccountName,mail | export-csv $FileName
Once you have a list of users with the correct list of Alias addresses I then ran the following PoweShell to update all of the proxy addresses
GC C:\temp\user.csv | % {
Set-ADUser $_ -Add @{ProxyAddresses="smtp:$_@aliasdomain.org.uk"}
}
Implementation of Mimecast – Outbound
G-Suite
To prepare your outbound G Suite hostname:
- Log on to the Google Admin Console.
- Navigate to Apps | G Suite | Gmail | Advanced Settings.
- Click on the Hosts button.
- Click on the Add Route button.
- Enter a Route Name (e.g. Mimecast Outbound Host).
- Select Multiple Host and enter the Mimecast Outbound Hostnames for your Mimecast region. Both must be marked as primary. See the “Outbound Send Connectors section of the Mimecast Gateway page for full details.
- Click on the Save button.
- Click on the Add Route button.
- Enter a Route Name (e.g. Internal Sending Host).
- Select Multiple Host and enter the Google Apps MX Records (ASPMX.L.GOOGLE.COM. and ALT1.ASPMX.L.GOOGLE.COM).
- Click on the Save button.
To configure routing rules:
- Click on the General Settings tab.
- Navigate to the Routing section.
- Click on the Configure button.
- Select the Outbound option in the “Messages to Affect” section.
- Select the Change Route option in the Route section.
- Select the Route Name created in step 5 of the “Preparing Your Outbound Hostname” section.
- Click on the Add Setting button.
- Click on the Add Another button.
- Select the Internal | Sending option in the “Messages to Affect” section.
- Select the Change Route option in the Route section.
- Select the Route Name created in step 9 of the “Preparing Your Outbound Hostname” section.
- Click on the Add Setting button.
Office 365
- Log in to the Office 365 Administration Console.
- Select the Admin | Exchange menu item.
- Select the Mail Flow | Connectors menu item.
- Create a Connector.
- Complete the New Connector – Select Your Mail Flow Scenario dialog as follows:
| From |
Select “Office 365” from the drop down list. |
| To |
Select “Partner Organization” from the drop down list. |
- Select the Next button.
- Complete the New Connector – New Connector dialog as follows:
| Name |
Enter a name for the connector. |
| Description |
Enter a description for the connector. |
| Turn It On |
Select this option to enable the connector. |
- Select the Next button.
- Select the Only When Email Messages are Sent to These Domains option.
- Select the
 icon to add the recipient domains that should use this connector.
icon to add the recipient domains that should use this connector.
- Enter a value of * to route all outbound emails through us.
- Select the OK button.

- Select the Next button.
- Select the Route Email Through These Smart Hosts option.
- Select the
 icon to add your region’s smart hosts.
icon to add your region’s smart hosts.

| Europe (Excluding Germany) |
eu-smtp-o365-outbound-1.mimecast.com
eu-smtp-o365-outbound-2.mimecast.com |
| Germany |
de-smtp-o365-outbound-1.mimecast.com
de-smtp-o365-outbound-2.mimecast.com |
| America |
us-smtp-o365-outbound-1.mimecast.com
us-smtp-o365-outbound-2.mimecast.com |
| South Africa |
za-smtp-o365-outbound-1.mimecast.co.za
za-smtp-o365-outbound-2.mimecast.co.za |
| Australia |
au-smtp-o365-outbound-1.mimecast.com
au-smtp-o365-outbound-2.mimecast.com |
| Offshore |
je-smtp-o365-outbound-1.mimecast-offshore.com
je-smtp-o365-outbound-2.mimecast-offshore.com |
- Select the Save button.
- Select the Next button.
- Select the following options:
- Always use Transport Layer Security (TLS) to Secure the Connection (recommended)
- Issued by a trusted certificate authority (CA)
- Select the Next button.
- Select the Next button.
- Add an Email Address of a recipient from a domain external to your organization.
- Select the Validate button.
- Select the Save button once Office 365 has successfully validated your settings.
Cloud Migrator Used for Data Migrations
Link to the 3rd Party Migration Tool:
https://cloudm.co/cloudmigrator?gclid=CjwKCAjwns_bBRBCEiwA7AVGHlIcjIAmgfI64swjBotgV_WwduBCpMhEaBjYrcruD30K1wuJPuIkERoC–wQAvD_BwE
So our experience with the Cloud Migrator APP has been interesting. Initially we started to use the Cloud Migrator Go SaaS application which was reasonably simple to configure following the guides provided by Cloud M. However we soon realised there were speed issues when moving data between G-Suite & O365. The issues are caused by the API’s between GSuite and O365 being limited. There is nothing we or Cloud M could do to improve the migration speed between the two services.
We then switched to the Cloud Migrator App which you install on your own dedicated server On Premise – in our case we used a Virtual machine in VMWare. Once configured we were able to fire up numerous Servers to run Cloud Migrator having a number of migration batches running at the same time and our Data throughput seemed to be 4x that of the cloud Migrator Go SaaS option.
All in all the customer is now running Co Existence of Office 365 and G-Suite. Mail is flowing and users are happy. We intend to complete the migration to Office 365 in the coming weeks. I decided to write this post as there does not seem to be many guides out there to help you migrate from G-Suite to Office 365. Hopefully if you read this it will help you on your projects.